Uk government and police servers susceptible to new Microsoft electronic mail hack, protection researchers say | Science & Tech Information
4 min readHackers are targeting Microsoft e-mail servers immediately after a sequence of vulnerabilities ended up thorough at a computer protection meeting earlier this thirty day period.
Though software updates for these vulnerabilities have been obtainable for months, extra than 50% of Microsoft Exchange servers in the Uk have not been up-to-date, according to stability researchers.
Among the servers still susceptible to attack are quite a few on the British government’s gov.united kingdom domain as effectively as the law enforcement.united kingdom domain utilised by forces in England, Wales and Northern Ireland.
Kevin Beaumont, a protection researcher who previously labored for Microsoft, criticised the firm for what he termed “knowingly dreadful” messaging to get shoppers to update their computer software.
The vulnerabilities are “as significant as they arrive”, wrote Mr Beaumont, as they make it possible for hackers to remotely execute code on an electronic mail server without the need of needing to enter a password.
Quite a few safety researchers and organisations have described detecting cyber criminals hacking into servers by exploiting this vulnerability and then deploying ransomware.
Although the flawed code was preset in April and May perhaps, Microsoft did not assign the challenges a CVE identifier (Common Vulnerabilities and Exposures) until finally July, delaying the solutions many organisations use to monitor and update vulnerabilities.
“Given numerous organisations vulnerability deal with through CVE, it produced a circumstance where by Microsoft’s clients have been misinformed about the severity of just one of the most vital company stability bugs of the 12 months,” Mr Beaumont wrote.
A spokesperson for Microsoft explained: “We introduced security updates to enable keep our customers harmless and guarded versus this assault approach.
“We suggest that shoppers adopt a strategy to be certain they are running supported versions of application and instantly put in protection updates as soon as probable following just about every regular safety launch,” they extra.
They stated they had very little to share in response to Mr Beaumont’s criticism about whether it had correctly communicated the value of installing these updates.
At the time that Microsoft issued a patch for the vulnerabilities there were being no publicly readily available proof of strategy exploits, which generally informs how critical a danger any provided vulnerability is viewed as to pose. It is really the distinction among being aware of Superman has a weakness, and really possessing some Kryptonite.
The CVE identifier was assigned in advance of the problem was technically in-depth at the Black Hat personal computer stability conference by a hacker who makes use of the take care of Orange Tsai.
It was centered on these complex specifics that other hackers have been able to build exploits allowing for them to recreate Orange Tsai’s strategies for accessing Exchange servers.
Orange Tsai stated they experienced learned additional vulnerabilities influencing Microsoft Trade which were “coming shortly” but did not respond to a Twitter message from Sky News for comment.
Mr Beaumont confirmed Sky Information how he experienced identified hundreds of unpatched Trade Servers in the United kingdom functioning the Outlook Website App, like quite a few on the gov.uk area and two on the law enforcement.uk domain.
The UK’s Nationwide Cyber Stability Centre explained to Sky News: “We are mindful of ongoing international action concentrating on previously disclosed vulnerabilities in Microsoft Exchange servers.
“At this stage we have not noticed evidence of British isles organisations becoming compromised but we continue on to monitor for impression.”
“The NCSC urges all organisations to install the most up-to-date security updates to guard on their own and to report any suspected compromises through our web page,” it additional.
A spokesperson for stability enterprise Mandiant informed Sky News they experienced noticed “a vary of industries” being hacked.
“It is hard to attribute this exercise to any 1 team of threat actors because various examples of evidence of principle exploit code have been made and released publicly by protection scientists,” the spokesperson stated.
“This signifies that any group could be leveraging the exploit and organisations who have not patched are vulnerable to assault,” they warned, including that patch costs “continue being low” and urging businesses to use patches as immediately as achievable.
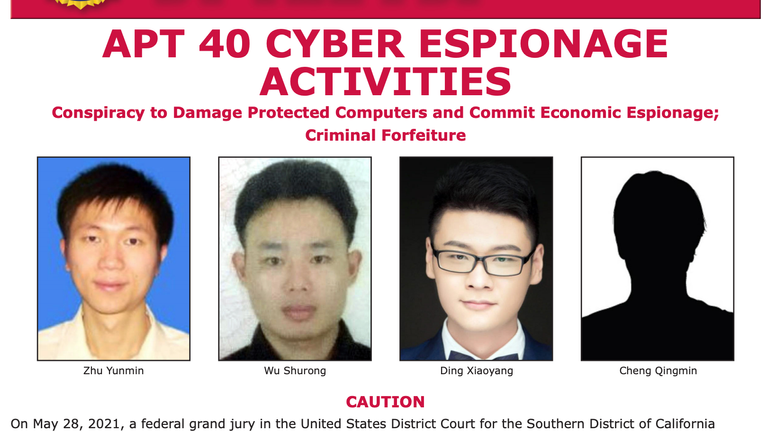
The new wave of attacks concentrating on Microsoft Trade servers follows Microsoft issuing a warning previously this year about a world-wide hacking campaign also concentrating on people servers which it attributed to point out-sponsored hackers based in China.
An estimated 400,000 servers all over the world have been “indiscriminately” compromised all through the espionage campaign.
The British authorities slammed the “reckless” methods applied by China as the strategy its cyber spies were making use of to keep access to sufferer servers also still left individuals servers open to criminals.
Whilst cyber espionage actors normally find to notice without disrupting their concentrate on networks, criminals will often disrupt the networks by deploying ransomware – building essential data files irretrievable except the victims pay back an extortion payment.
Final thirty day period, the United kingdom and allies accused China of “systematic cyber sabotage” in link with that marketing campaign.
At the exact time, the contractors made use of by Beijing’s cyber intelligence apparatus ended up accused of conducting “unsanctioned cyber functions globally… for their individual personalized profit” but it is not distinct whether these unsanctioned operations were centered on exploiting the entry established by the sanctioned espionage campaign.